In today's interconnected world, accessing IoT devices securely behind a firewall from a Mac without incurring additional costs has become a necessity. As more organizations and individuals adopt IoT technologies, ensuring secure and efficient connectivity is crucial. This article will guide you through the process of logging into IoT devices behind firewalls using AWS for free on a Mac, ensuring you stay protected while leveraging the power of cloud computing.
Whether you're managing home automation systems, monitoring industrial equipment, or accessing remote sensors, secure connectivity is paramount. This article will provide step-by-step instructions, expert tips, and best practices to ensure your IoT devices remain accessible and secure, even when protected by a robust firewall.
By the end of this guide, you'll have a comprehensive understanding of how to leverage AWS services for free to establish secure connections between your Mac and IoT devices. Let's dive in!
Read also:Eilish Mccolgan A Rising Star In The World Of Athletics
Table of Contents
- Introduction to IoT Device Security
- Understanding Firewalls and Their Role
- AWS Free Tier: What You Need to Know
- Connecting IoT Devices Behind Firewalls
- Setting Up Your Mac for IoT Access
- AWS Services for IoT Connectivity
- Security Best Practices for IoT Devices
- Troubleshooting Common Issues
- Cost Considerations and Free Options
- Conclusion
Introduction to IoT Device Security
IoT devices are revolutionizing the way we interact with technology, but they also introduce new security challenges. Ensuring secure access to these devices, especially when they are protected by firewalls, requires a strategic approach. The integration of cloud services like AWS provides a robust solution for managing IoT devices securely and efficiently.
Using AWS for free allows users to leverage advanced security features without breaking the bank. This section will explore why security is critical for IoT devices and how AWS can help mitigate risks associated with remote access.
Why Security Matters for IoT Devices
IoT devices often handle sensitive data, making them prime targets for cyberattacks. By implementing proper security measures, such as using firewalls and secure protocols, you can protect your devices from unauthorized access.
- Prevent data breaches
- Protect sensitive information
- Ensure device integrity
Understanding Firewalls and Their Role
A firewall acts as a barrier between your network and external threats. It monitors and controls incoming and outgoing network traffic based on predetermined security rules. For IoT devices behind firewalls, accessing them remotely requires careful configuration to maintain security.
Firewalls are essential for protecting IoT devices from unauthorized access. This section will explain how firewalls work and how they can be configured to allow secure remote access.
Types of Firewalls
There are several types of firewalls, each with its own strengths and weaknesses. Understanding the differences can help you choose the right solution for your needs.
Read also:Emily Carriveau Divorce Understanding The Legal And Emotional Aspects
- Packet-filtering firewalls
- Stateful inspection firewalls
- Application-level gateways
AWS Free Tier: What You Need to Know
AWS offers a free tier that provides access to a wide range of services, including those useful for IoT device management. This section will outline the benefits of using AWS Free Tier and how it can be utilized for secure IoT access.
With AWS Free Tier, you can experiment with various services without incurring costs. This makes it an ideal solution for individuals and small businesses looking to manage IoT devices securely.
Key Features of AWS Free Tier
- Free access to core AWS services
- Limited usage for one year
- Perfect for testing and development
Connecting IoT Devices Behind Firewalls
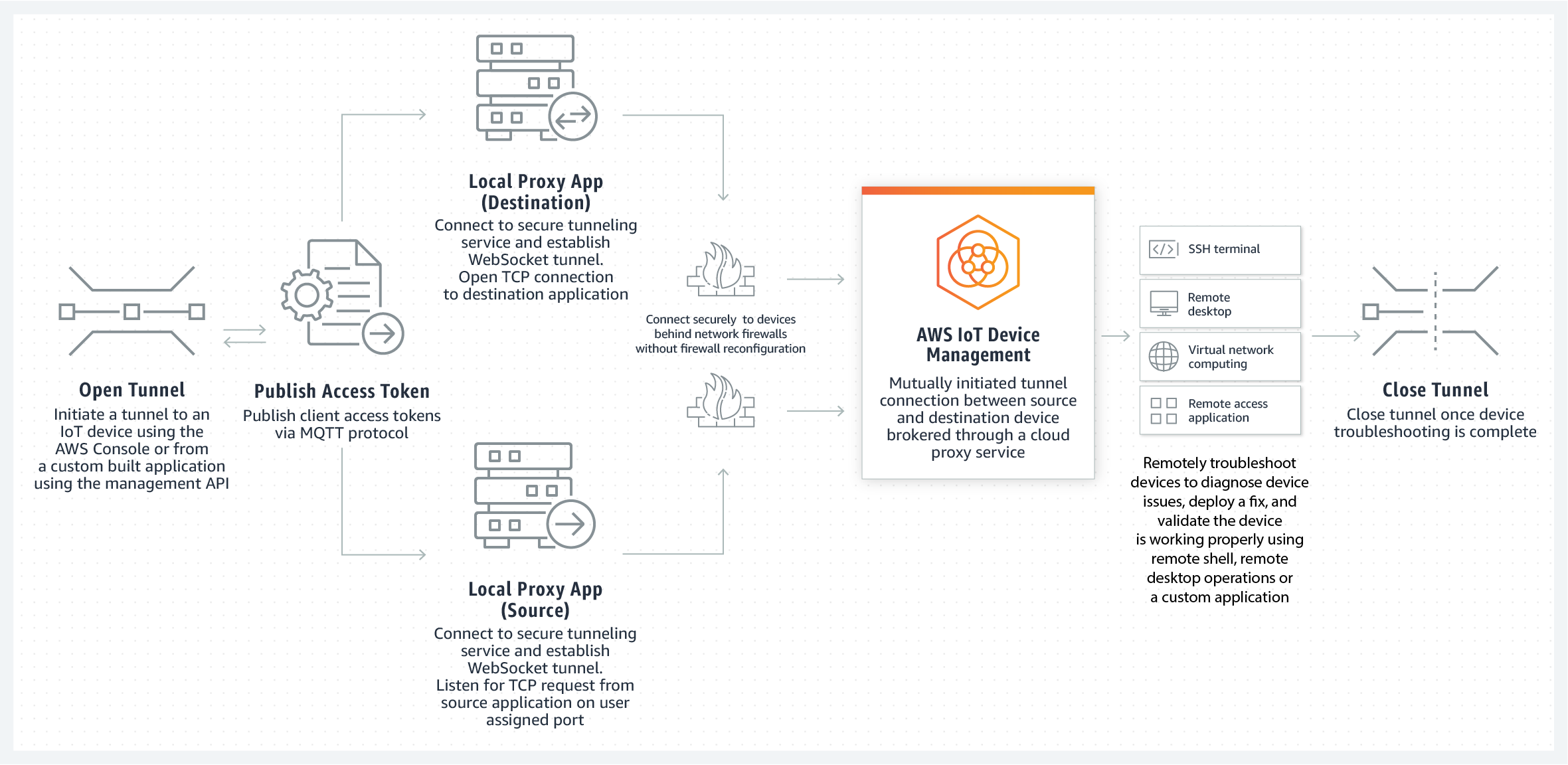
Connecting IoT devices behind firewalls requires a strategic approach to ensure security and efficiency. This section will guide you through the process of establishing secure connections using AWS services.
By leveraging AWS IoT Core and other related services, you can create a secure tunnel for accessing your devices without compromising security.
Steps to Connect IoT Devices
- Set up an AWS account
- Create an IoT thing in AWS IoT Core
- Configure firewall rules
- Establish a secure connection
Setting Up Your Mac for IoT Access
Your Mac plays a crucial role in accessing IoT devices securely. This section will provide step-by-step instructions for configuring your Mac to work seamlessly with AWS services.
From installing necessary software to configuring network settings, this guide will ensure your Mac is ready for IoT device management.
Software Requirements
- AWS CLI
- Secure shell (SSH) client
- Browser with AWS console access
AWS Services for IoT Connectivity
AWS offers a variety of services tailored for IoT connectivity. This section will explore the key services that can be used to manage IoT devices securely and efficiently.
By utilizing services like AWS IoT Core, AWS Lambda, and Amazon S3, you can create a robust infrastructure for managing IoT devices.
Key AWS Services
- AWS IoT Core
- AWS Lambda
- Amazon S3
Security Best Practices for IoT Devices
Implementing security best practices is essential for protecting IoT devices. This section will provide expert tips and strategies for securing your devices and ensuring safe remote access.
From using strong passwords to enabling two-factor authentication, these practices will help you maintain the highest level of security for your IoT devices.
Tips for Securing IoT Devices
- Use strong, unique passwords
- Enable two-factor authentication
- Regularly update firmware
Troubleshooting Common Issues
Even with the best planning, issues can arise when connecting IoT devices behind firewalls. This section will address common problems and provide solutions to help you overcome them.
From network configuration errors to AWS service limitations, this guide will help you troubleshoot and resolve issues quickly.
Common Issues and Solutions
- Firewall blocking connections
- Incorrect AWS configuration
- Network latency
Cost Considerations and Free Options
While AWS offers a free tier, it's important to understand the potential costs associated with using AWS services for IoT device management. This section will explore cost considerations and highlight free options available to users.
By carefully managing your usage and selecting the right services, you can keep costs low while maintaining high levels of security and performance.
Managing Costs with AWS
- Monitor usage regularly
- Choose cost-effective services
- Utilize free tier benefits
Conclusion
In conclusion, accessing IoT devices behind firewalls on a Mac for free using AWS is both feasible and secure. By following the steps outlined in this guide, you can ensure your devices remain protected while maintaining efficient connectivity.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT security and AWS services. Together, let's build a safer and more connected world!
Data Source: AWS Free Tier | AWS IoT Core Documentation