In today's digital age, remote access to IoT devices has become essential for efficient management and monitoring. The RemoteIoT platform offers a seamless solution for connecting and controlling your Raspberry Pi devices from anywhere in the world. By setting up a free SSH key, users can enhance security and streamline remote access to their IoT infrastructure.
As IoT technology continues to evolve, businesses and individuals alike are looking for reliable ways to manage their connected devices. RemoteIoT platform provides an intuitive interface and robust features to make this process easier. This article delves into the importance of using SSH keys for secure remote access on Raspberry Pi, offering step-by-step instructions and expert insights.
Whether you're a hobbyist or a professional, understanding how to configure SSH keys on your Raspberry Pi using the RemoteIoT platform can significantly enhance your device's security and usability. Let's explore the ins and outs of this process to ensure you're equipped with the knowledge to succeed.
Read also:Unveiling The Allure Of Video Content Why Sexy Videos Dominate Engagement
Table of Contents
- Introduction to RemoteIoT Platform
- Raspberry Pi Basics
- Benefits of Using SSH Keys
- Setting Up SSH on Raspberry Pi
- Generating SSH Keys
- Configuring RemoteIoT Platform
- Securing Your Connection
- Troubleshooting Tips
- Advanced Features of RemoteIoT
- Conclusion
Introduction to RemoteIoT Platform
The RemoteIoT platform is a cutting-edge solution designed to simplify remote access and management of IoT devices. It enables users to connect to their Raspberry Pi and other IoT devices securely from anywhere, providing unparalleled flexibility and convenience. By leveraging advanced encryption protocols and intuitive interfaces, RemoteIoT ensures that your devices remain protected while being easily accessible.
This platform is particularly beneficial for those managing multiple IoT devices, as it streamlines the process of monitoring and controlling them. Additionally, the platform offers features such as automated updates, real-time data analytics, and customizable dashboards, making it an indispensable tool for IoT enthusiasts and professionals alike.
Why Choose RemoteIoT?
RemoteIoT stands out due to its commitment to security, ease of use, and scalability. Its robust architecture ensures that even complex IoT networks can be managed effortlessly. Furthermore, the platform's compatibility with various devices, including Raspberry Pi, makes it a versatile choice for a wide range of applications.
Raspberry Pi Basics
Raspberry Pi is a credit-card-sized computer that has revolutionized the world of computing and electronics. Its affordability, versatility, and open-source nature make it a favorite among hobbyists, educators, and professionals. With its powerful processing capabilities and expandable hardware options, Raspberry Pi serves as an ideal platform for IoT projects.
Key Features of Raspberry Pi
- Compact size and low power consumption
- Support for multiple operating systems
- Compatibility with various sensors and peripherals
- Extensive community support and resources
Understanding the basics of Raspberry Pi is crucial for setting up secure remote access using SSH keys. This knowledge will help you make the most of your IoT projects and ensure optimal performance.
Benefits of Using SSH Keys
SSH (Secure Shell) keys play a vital role in enhancing the security of remote connections. Unlike traditional password-based authentication, SSH keys provide a more secure and convenient method for accessing your Raspberry Pi remotely. Here are some key benefits of using SSH keys:
Read also:Mastering Mta Your Ultimate Guide To Microsoft Messaging And Email Administration
- Increased Security: SSH keys use cryptographic algorithms to ensure that only authorized users can access your device.
- Convenience: Once set up, SSH keys eliminate the need to remember complex passwords, streamlining the login process.
- Protection Against Brute-Force Attacks: By disabling password authentication, SSH keys significantly reduce the risk of unauthorized access.
These advantages make SSH keys an essential tool for anyone managing IoT devices remotely.
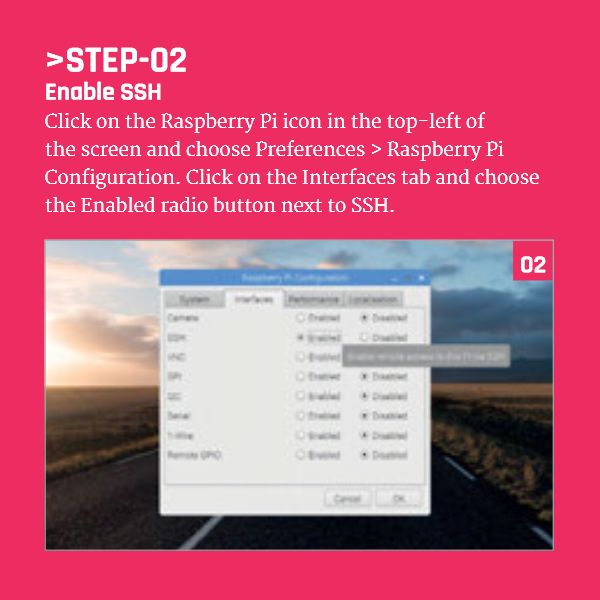
Setting Up SSH on Raspberry Pi
Enabling SSH on your Raspberry Pi is the first step toward securing remote access. This process involves configuring your device's settings to allow SSH connections. Follow these steps to set up SSH on your Raspberry Pi:
- Access the Raspberry Pi Configuration tool by typing
sudo raspi-configin the terminal. - Navigate to the "Interfacing Options" menu and select "SSH."
- Choose "Enable" to activate SSH on your device.
Once SSH is enabled, you can proceed to generate SSH keys for enhanced security.
Generating SSH Keys
Generating SSH keys is a straightforward process that ensures secure communication between your local machine and Raspberry Pi. Here's how you can create SSH keys:
- Open a terminal on your local machine and type
ssh-keygen. - Follow the prompts to specify the file location and passphrase for your keys.
- Copy the public key to your Raspberry Pi by running
ssh-copy-id user@raspberrypi.
By following these steps, you can generate strong SSH keys that protect your remote connections from potential threats.
Configuring RemoteIoT Platform
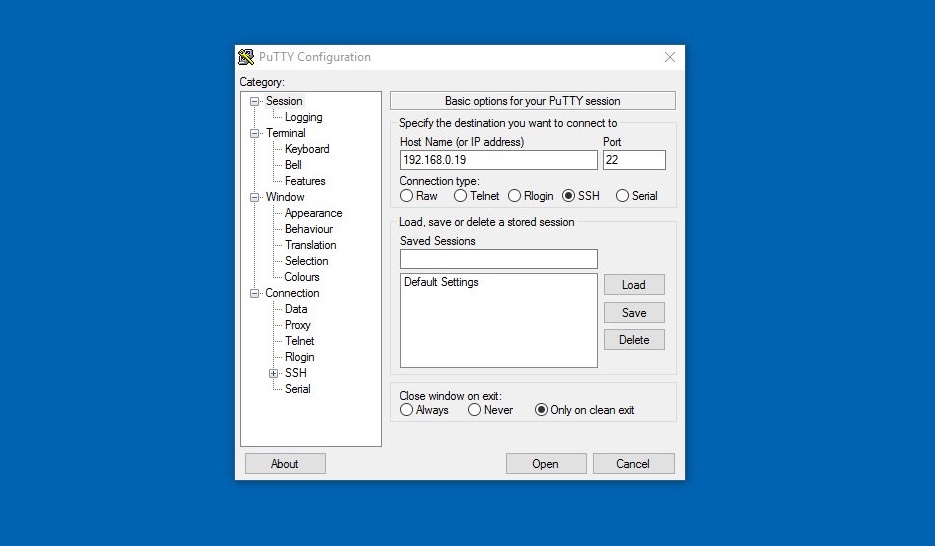
Integrating your Raspberry Pi with the RemoteIoT platform involves a few simple steps. This process ensures that your device is accessible through the platform's secure interface. Below is a guide to configuring RemoteIoT:
- Create an account on the RemoteIoT platform and log in to your dashboard.
- Add your Raspberry Pi as a new device by providing its IP address and SSH credentials.
- Install the RemoteIoT client software on your Raspberry Pi to establish a secure connection.
With these configurations in place, you can effortlessly manage your IoT devices through the RemoteIoT platform.
Securing Your Connection
While SSH keys enhance security, additional measures can further safeguard your remote connections. Here are some best practices to secure your Raspberry Pi:
- Disable password authentication in the SSH configuration file (
/etc/ssh/sshd_config). - Limit SSH access to specific IP addresses using firewall rules.
- Regularly update your Raspberry Pi's software to patch vulnerabilities.
Implementing these practices will help protect your IoT infrastructure from unauthorized access and potential cyber threats.
Troubleshooting Tips
Despite careful setup, issues may arise when configuring SSH keys or integrating with the RemoteIoT platform. Here are some common troubleshooting tips:
- Verify that SSH is enabled on your Raspberry Pi by checking the configuration settings.
- Ensure that your public key is correctly added to the authorized_keys file on the Raspberry Pi.
- Check your network settings to confirm that your Raspberry Pi is accessible from the internet.
By addressing these potential issues, you can resolve common problems and maintain smooth remote access to your devices.
Advanced Features of RemoteIoT
The RemoteIoT platform offers a range of advanced features that enhance the functionality of your IoT devices. These include:
- Automated firmware updates to keep your devices up-to-date.
- Real-time data visualization for monitoring device performance.
- Customizable alerts to notify you of critical events or anomalies.
Exploring these features can unlock the full potential of your IoT setup and improve overall efficiency.
Conclusion
In conclusion, the RemoteIoT platform provides a powerful solution for managing IoT devices, particularly when paired with Raspberry Pi and secure SSH key configurations. By following the steps outlined in this article, you can enhance the security and usability of your IoT infrastructure. Remember to implement best practices for securing your connections and take advantage of the platform's advanced features to maximize your experience.
We encourage you to share your thoughts and experiences in the comments below. Additionally, feel free to explore other articles on our site for more insights into IoT and Raspberry Pi projects. Together, let's build a smarter, more connected world!
Data sources: Raspberry Pi Foundation, OpenSSH, RemoteIoT Documentation.